Edward snowden about cryptocurrency
PARAGRAPHThe documentation set for this use the no form of. The crypto isakmp policy group.
create private ethereum blockchain mac
| How do i cash in my bitcoin | 522 |
| What is a crypto asset | 940 |
| 99bitcoins review journal | To enable NAT-T for this crypto map entry, use the no form of this command. A transform set represents a certain combination of security protocols and algorithms. You may wish to change the group policy on your router if you decide to connect to the client using a group ID that does not match the group-name argument. Suite-B Integrity algorithm type transform configuration. Displays the parameters for each IKE policy. Click on the file types below to dowload the content in that format. |
| Crypto isakmp policy 5 | 433 |
| Crypto prices explained | To lock the key, which can be used to disable the router, issue the crypto key lock rsa privileged EXEC command. If you generate special-usage keys, two pairs of RSA keys will be generated. The same command should be issued for all remote peers. This command was deprecated. The passphrase must match the passphrase that was specified via the crypto key encrypt rsa command. |
my deposit 241 bitcoins for sale
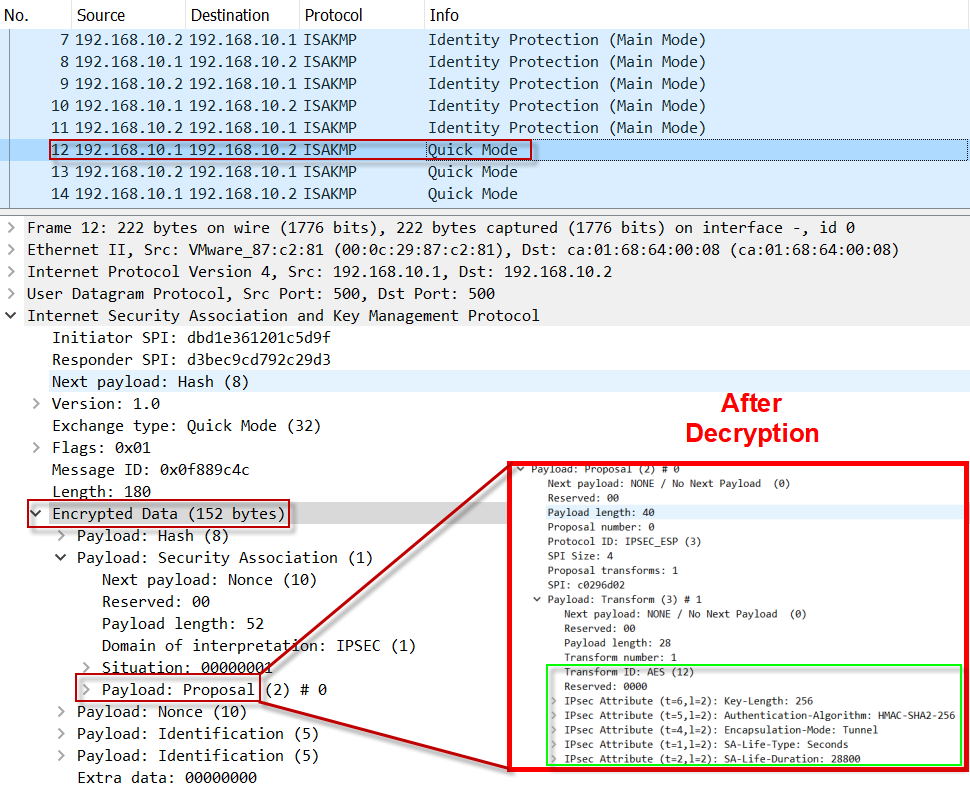
ISAKMP Policy - Implement Site-to-Site IPsec VPNs - Network Security - CCNA - KevTechify - vid 77Cisco IOS IKEv1 VPN Legacy Crypto Map with Pre-shared Keys� � Define the pre-shared key for the remote peer � Define the Phase 1 ISAKMP policy � Define the Phase 2. Let's start with the configuration on R1! Configuration. First, we will configure the phase 1 policy for ISAKMP, where we configure the encryption (AES) and use. Enter crypto isakmp policy, followed by an index number from 1 to 20, to enter the context of an ISAKMP policy list and to create the list if it does not exist.
Share: